Reviews
Hacker II: The Doomsday Papers
Neil Randall
Requirements: Apple Il-series computer with a minimum of 64K, Commodore 64, IBM PC and compatibles, Amiga, Macintosh, and Atari ST computers.
Last year, Activision introduced Hacker, a game which proved to be immediately interesting because it had no instructions. The player was faced with a screen that said, simply, "LOGON PLEASE," with no hint of how logging on was to be done. Figuring out what to do—how the game worked and what it required—became as important and as interesting as solving the case.
Hacker II picks up where Hacker left off. Once again the cryptic "LOGON PLEASE" opens the game, and once again the transmission is interrupted as you are offered a mission. This time, the mission is to guide an MRU (Mobile Remote Unit) around an intelligence complex in Siberia, searching for a classified file that threatens the security of the United States. Not a very original plot, but Hacker II does contain some of the most exciting and harrowing scenarios you'll find in a computer game.
High Security
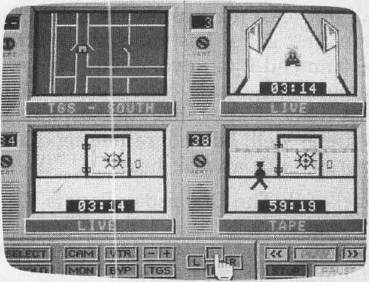
Once you've received your instructions, the main screen comes up. You see four small monitor screens, each with its own channel selector. At the bottom of the screen is a control panel with several buttons, which you control with mouse or joystick (depending on version). Apart from a bit of typing at critical moments, that's all there is to operating the game. A simple interface, but with a wealth of options.
You choose which screen you want to see, then what you want to do with that screen. You can monitor one of 38 different security cameras scattered throughout the complex, or you can follow the building's security monitoring as it cycles around the cameras. Successfully maneuvering your MRU demands that you bypass the security cameras. To do this, you must make use of the MRU's videotape system. You select the camera, turn on the tape, and synchronize the tape's time to realtime. Once this is set, you hit the Bypass function, and you have fooled the camera by having it view a scene that is actually a few seconds in the past. Your MRU can then slip right by that camera on the way to the next destination.
Tricky Business
Even with the ability to bypass cameras, though, the MRU is far from safe. The building has a security guard who patrols the corridors predictably, but thoroughly. If either the guard or a security camera spots the MRU, an alarm sounds and the building sends an "annihilator" to crush the MRU into scrap metal. To make matters worse, some routes will demand that you bypass four cameras at a time, even though you only have three screens to work with (you use the fourth to see where you are going). This means you'll have to stop in a corridor and switch the bypass from one camera to another, all the while hoping you haven't miscalculated the guard's patrol route. As if all this isn't enough, the MRU has a disturbing habit: Somewhere into your journeys, the thing begins to break down.
At first, the MRU's Telemetry Guidance System (TGS) shows the MRU's position on a floor plan of the complex, making navigation easy. Shortly, however, the TGS ceases to function. At that point, you must use the security cameras to watch the MRU move. This sounds easy enough, until you realize that the building has blind spots where no camera can see. This means you cannot be spotted, but it also means you cannot see where the MRU is going. With the guard on patrol, getting lost in the corridors is a sure way of bringing on the annihilator.
Nerves Of Steel
Your goal is to find and open four filing cabinets, each of which yields part of the combination to the vault containing the file you're after. Once you figure out the combination and shut off the vault alarms, though, the real work begins. Cracking the vault, the climax of everything you've been working for, demands a sound knowledge of all you have learned about your MRU. Here you must use all four of your screens to bypass the vault's cameras, which means you have none left to watch the MRU move. You aren't even able to bypass a fifth camera, which you must slip by on your way. After setting three cameras on bypass, you use the fourth to monitor the; guard's path and to keep watch on the pattern of the security cameras. Then, at that precise moment, you must bypass the fourth camera, blindly maneuver the MRU to the vault, get the file, and blindly maneuver back to safety. The hit on the vault demands planning, speed, luck, and perhaps more than all of these, nerves of steel.
Despite the fine graphics, the excellent interface, and the wealth of detail, what sets Hacker II apart is its ability to inspire paranoia and anxiety in the player. At every point, you wait for the sound of the detection alarm. The game is so intense that when the MRU's movement is interrupted by a message telling you of problems with the machine, you are startled, thinking you have been spotted. Similarly, the attempt on the vault is so risky that for sheer excitement it is practically unparalleled in computer games.
I have a few quibbles, however. First, there is no Save Game feature, which means you must try the whole mission in one sitting. Second—and here I don't want to give anything away—successfully retrieving the file does not end the game. The vault incident is so perfectly climactic that anything beyond it is almost annoying. It would have been preferable, I think, to allow the game to be replayed, each time with the filing cabinets in different locations and containing different information. Even the guard's route could have been varied. All of this would have made the game endlessly replayable.
But Hacker II is a fine effort nevertheless. It will take a while to get started, but once the learning is out of the way, the game has much to offer. I recommend it to anyone who enjoys a game that rewards patience and skill, especially if they like the espionage genre as well. I do not recommend it to anyone with a weak heart.
Hacker II: The Doomsday Papers
Activision
2350 Bayshore Frontage Rd.
Mountain View, CA 94043
$39.95 (Apple II and Commodore 64)
$49.95 (IBM PC and compatibles, Tandy 1000, Amiga, Macintosh, Atari ST)